Earlier today, talented developer alephzain described a security vulnerability affecting most if not all Exynos 4 devices, which represent dozen of millions gadget out there.
Unfortunately he also released a working exploit with complete source code before the various vendors affected (Samsung, Meizu and surely others) were made aware of it, leading to a severe security issue without accessible fix for now.
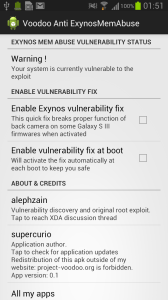
I wrote then an application to circumvent the issue while manufacturer patch the security hole and publish OTA updates.
However, please note its a partial fix that cannot secure completely your device which is to date impossible without modifying it − an operation that will stop the ability to install OTAs without an external tool.
That’s why I would still recommend to consider Chainfire’s solution linked below.
Characteristics of this app:
- Works on any device, let you know if your system is vulnerable
- Doesn’t require root to apply the fix
- Doesn’t modify your system, copy files or flash anything
- Fix can be enabled or disable at will
- Free of charge
Limitations:
- Break proper function of the Front camera on some Galaxy S III and Galaxy Note II Samsung official firmwares when activated.
Workaround: enable HDR or Low light photography camera mode. Both blend multiple exposures. - Might alter MHL/HDMI output functions on some devices (not confirmed)
- Cannot protect efficiently against some potential attacks (typically, on boot).
The real fix by manufacturers or some carefully written custom kernels will indeed be the only true solutions to this vulnerability − and won’t introduce any feature regression like this one does with some firmwares on cameras. - Comes without any kind of support or warranty.
Download link:
version 0.9
- Circumvent a random behavior nature in the exploit and try harder in case of initial failure to apply the fix at boot.
Recommended update.
version 0.8
- Notify the user in case the application was unable, for any reason, to apply the fix (you need to enable it manually then)
Recommended update.
version 0.7
- Improve efficiency if the apply on boot feature by some modifications after study of earlier versions published by Chainfire.
Recommended update.
version 0.6
- Minor: remove unused asset to reduce application size of 16kB.
version 0.5
- Add camera HDR or Low Light capture modes workaround tip in fix description.
version 0.4
- Add missing Internet permissions for Flurry analytics:
I will likely share installation figures with my Samsung security contacts, so they get an idea of the interest generated by this kind of early fix. - Clarify apply on boot limitations.
version 0.3
- Increase the chances to run early at boot.
- Improve descriptions.
version 0.2
- Fix link to this page inside the app.
First version, 0.1
Notes:
- There’s an XDA-forums thread for feedback.
- Chainfire made an app easily rooting your device instead (this app has no relation with rooting whatsoever)
Credits to him too as it was fun sharing mind when reading the exploit earlier today. - Redistribution of this APK outside of this web page is forbidden, please link this web page directly that I’ll keep updated.
- This application is not released on Google Play because it use the vulnerability itself as test and tool to protect against itself (yes ^^)

[…] Go to Source – اضغط هنا لمشاهدة الموضوع كامل Project Voodoo […]
App causes me I can’t turn on the camera and do not play videos in Youtube app. Samsung Galaxy S2 CM9.1
[…] Além do Galaxy S III, a vulnerabilidade que poderia permitir o roubo de dados também está presente em outros aparelhos com processadores Exynos 4210 e Exynos 4412: Galaxy S II, Galaxy S III, Galaxy Note, Galaxy Note II, Galaxy Player, Galaxy Camera, Galaxy Tab 2 e Galaxy Note 10.1, além do Meizu MX 4-core. Se você não quiser esperar a atualização da Samsung, há um patch extraoficial. […]
[…] خبيثة ومن ثم قام أحد المطورين […]
[…] third celebration patch wаѕ fast mаdе accessible bу Supercurio thаt bound thе issues, […]
[…] تعطيل الجهاز و إجراء نشاطات مشبوهة بطريقة خبيثة ومن ثم قام أحد المطورين بحل المشكلة من خلال تحميل ملف وتركيبه على […]
[…] Além do Galaxy S III, a vulnerabilidade que poderia permitir o roubo de dados também está presente em outros aparelhos com processadores Exynos 4210 e Exynos 4412: Galaxy S II, Galaxy S III, Galaxy Note, Galaxy Note II, Galaxy Player, Galaxy Camera, Galaxy Tab 2 e Galaxy Note 10.1, além do Meizu MX 4-core. Se você não quiser esperar a atualização da Samsung, há um patch extraoficial. […]
[…] تعطيل الجهاز و إجراء نشاطات مشبوهة بطريقة خبيثة ومن ثم قام أحد المطورين بحل المشكلة من خلال تحميل ملف وتركيبه على […]
[…] Além do Galaxy S III, a vulnerabilidade que poderia permitir o roubo de dados também está presente em outros aparelhos com processadores Exynos 4210 e Exynos 4412: Galaxy S II, Galaxy S III, Galaxy Note, Galaxy Note II, Galaxy Player, Galaxy Camera, Galaxy Tab 2 e Galaxy Note 10.1, além do Meizu MX 4-core. Se você não quiser esperar a atualização da Samsung, há um patch extraoficial. […]
[…] تعطيل الجهاز و إجراء نشاطات مشبوهة بطريقة خبيثة ومن ثم قام أحد المطورين بحل المشكلة من خلال تحميل ملف وتركيبه على […]
[…] تعطيل الجهاز و إجراء نشاطات مشبوهة بطريقة خبيثة ومن ثم قام أحد المطورين بحل المشكلة من خلال تحميل ملف وتركيبه على […]
[…] تعطيل الجهاز و إجراء نشاطات مشبوهة بطريقة خبيثة ومن ثم قام أحد المطورين بحل المشكلة من خلال تحميل ملف وتركيبه على […]
[…] تعطيل الجهاز و إجراء نشاطات مشبوهة بطريقة خبيثة ومن ثم قام أحد المطورين بحل المشكلة من خلال تحميل ملف وتركيبه على […]
[…] seguida buscaron una solución y la colgaron en su foro. También la gente de Project Voodoo dio su propia solución que además no requería ser root. Evidentemente avisaron a la compañía surcoreana y esta tras un […]
[…] تعطيل الجهاز و إجراء نشاطات مشبوهة بطريقة خبيثة ومن ثم قام أحد المطورين بحل المشكلة من خلال تحميل ملف وتركيبه على […]
[…] third party patch was quickly made available by Supercurio that fixed the issues, and Samsung told us they would be […]
[…] بكل بساطة أن تحميل التطبيق Supercurio الذي سيعمل من غير الحاجة إلى عملية الروت و سيقوم […]
[…] third party patch was quickly made available by Supercurio that fixed the issues, and Samsung told us they would be […]
[…] third party patch was quickly made available by Supercurio that fixed the issues, and Samsung told us they would be […]
[…] third party patch was quickly made available by Supercurio that fixed the issues, and Samsung told us they would be […]
[…] ve Samsung’u beklemekte sabırsız davranan, ayrıca ne yaptığını bilen kullanıcılar bu bağlantıyı takip ederek söz konusu çözüme […]
[…] Wer sein Android-Gerät bis dahin besser absichern will, kann beispielsweise die kostenlose App Instant Anti Exynos Mem Abuse verwenden. Die App lässt sich auch auf nicht gerooteten Geräten einsetzen. Der Fix kann bei […]
thank
Thank you so much for your work! Merry Christmas and a peaceful, healthy new year!
San
jh
I am assuming the fix when disabled restores camera functionality?
ok
Samsung S2+3 Sicherheitslücke provisorisch behoben !!
Auf der Seite … (http://project-voodoo.org/articles/instant-fix-app-for-exynos-mem-abuse-vulnerability-no-root-required-reversible)
den Link für Version 0.9 benutzen … (http://dl.project-voodoo.org/apps/Voodoo-instant-anti-exynos-mem-abuse-0.9.apk)
Hier noch der Artikel mit Stellungsnahme seitens Samsung:
http://www.pcwelt.de/news/Android-Schwere_Sicherheitsluecke_in_Samsung-Smartphones-7302465.html?r=8626617208807744&lid=217084&pm_ln=39
كيف يمكنني إن اكتشف مثل هذه الحالات التي انتم قمتم بإصلاحات
Thank you for the patch, but when activated my SGS2 cameras are not working at all unless I am disabling it. I hope that there’ll be a fix soon for my custom ROM.
Same issue here on gs2 – int version – but thanx for this
All good, camera working now, disabled then enabled…
http://project-voodoo.org/articles/instant-fix-app-for-exynos-mem-abuse-vulnerability-no-root-required-reversible
Avast, as of now, blocks the installation of the fix?!!
Is this a false positive???
Where is Samsung with a comment?
Exynos 處理器安全性問題,各位臉書應該都有朋友在轉吧? 我來說說自己的想法給各位參考。
http://project-voodoo.org/articles/instant-fix-app-for-exynos-mem-abuse-vulnerability-no-root-required-reversible
Thx for your work mate !
Okay the fix makes the Camera screen turn green but once captured the image shows as normal.
It is only stop the camera feed to the screen but everything else still working accordingly.
Hope this answering some of others question. Camera still functioning just didn’t display preview on screen.
Problema afetaria Galaxy S II, Galaxy S III, Galaxy Note e Note 2.
Hello Supercurio, I just tried your quick fix, but it appears that my camera works with it turned on. My phone is a SCH-I605.
Version 0.5 have a WIRUS !!!
SGS3, UK 4.1.1 stock – i confirm both cameras working after patch active and reboot.
Galaxy Tab 7 Plus tablet user here and guest what, we also are affected for this exploit, using this app fix it but also break the camera, I hope you, or other dev could find a fix to this, thanks.
Yup that’s right, Galaxy Tab 7 Plus also use an Exynos 4 platform and rocks very similar drivers.
The fixes will be released by Samsung, what I published here can more be seen as a workaround, with concrete limitations due to its “don’t modify anything” implementation.
NT7000 – installed 0.9 and camera is black and crashes after a minute. I have Android 4.0.4 and build LRI.
Stopping and Disinstalling did not change it. After reboot camera ok again.
I did not find the low light fix, as camera stops responding and hangs.
Just wanted to say I didn’t enable this and then try the exploit app, I had done the exploit and tested both cameras, and then enabled your app and tried both cameras again, and in all cases both cameras worked on my sgs 3 gt-i9300 on stock 4.1.1 (rooted via exploit before enabling your fix for camera testing)